TECHNOLOGY The Government warns about a serious security problem in Windows: this is how you can solve it
SECURITY. The month of the Stations of the Cross for Adeslas patients after a cyberattack: "They don't even know how to tell me the price of my treatment"
The National Cybersecurity Institute (INCIBE) has detected a campaign to send fraudulent emails that try to
impersonate Correos y Telégrafos
.
For this reason, the Incibe (dependent on the Ministry of the Economy) has issued an alert of high importance (level 4/5) warning about this usurpation that in fact seeks to spread a malicious Trojan-type program on the computers of its victims.
Trojan-type programs are files (apparently innocuous) that actually
hide malicious code
that allows the attacker to access his victim's computer remotely.
Its name is inspired by the wooden horse full of soldiers that the Greeks built to gain access to the interior of Troy and
open the gates of the walls
.
In the scam identified by Incibe, victims receive an email with the subject "
Order Returned
- [id (random numbers)]".
The message informs that an attempt has been made to deliver a package but that it has not been possible.
Therefore, a period of 3 days is provided for you to reschedule the delivery and
a payment of 3.40 euros is required
.
The Incibe warns that the emails contain
a link that pretends to be from the Correos customer area
, and once the user has clicked on the link, they are redirected to a web page created by the criminals where the malicious program will be downloaded.
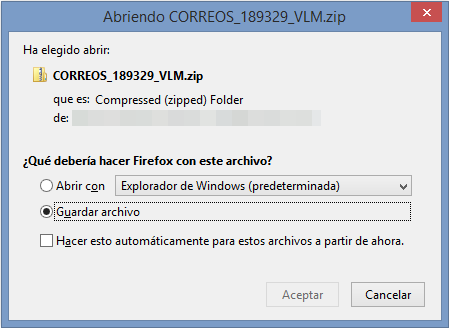
The
names
of the malicious files are: CORREOS_000000_XXX.zip
"Every time
the file
is
downloaded
, it has a random name, although it follows the same pattern:« POST_ + 5 or 6 random numbers + _ + 3 random letters »", says the Incibe.
In the campaign detected by this public body, the email tries to distribute a type of
malware
, identified as
Trojan Downloade
r or Dropper, specially designed to take control of the victim's computer.
Once the Trojan has taken control of the infected terminal, criminals have a
free hand to steal personal data
or re-infect the computer with other malicious programs, depending on their objectives.
Identity fraud
To do this, cybercriminals make use of the technique known as email spoofing, with which they
simulate that the sender of the email is the Correos group
, when in reality it is not.
"The body of the message contains multiple grammatical and spelling errors along with other
incongruities
, something that a legitimate entity would never commit," says Incibe.
Once the victim has clicked on the attached link, the browser opens to download the malicious file "which
may be detected by some browsers
as a malicious file, notifying the user," they indicate from the Institute of Cybersecurity.
What to do to protect yourself from this type of fraud?
To prevent our computer equipment from being affected by this type of
fraud
, the National Cybersecurity Institute periodically provides a series of recommendations in this regard, such as:
Do not open emails from unknown users or that you have not requested: delete them directly.
Do not reply in any case to these emails.
Check the links before clicking, even if they are from known contacts.
Be wary of shortened links.
Be wary of attached files, even if they are from known contacts.
Always keep your operating system and antivirus updated.
In the case of antivirus, check that it is active.
Make sure your employees' user accounts use strong passwords and do not have administrator permissions.
According to the criteria of The Trust Project
Know more
tangled
EmpresasCorreos launches a campaign to claim the consumption of local products
The small print of the patriotic campaign of Correos: "Proud of ours" ... but made in China
Boiling water, beeps and error messages: how a hacker can hijack a smart coffee maker
See links of interest
Last News
TV programming
English translator
Work calendar
Movies TV
Topics
Live, the queen stage of the Giro: Pinzolo - Laghi di Cancano
Live, follow the stage between Lodosa and Laguna Negra
Stage 2 of the Vuelta, live: Pamplona - Lekunberri
HNK Rijeka - Real Sociedad
PSV - Granada CF